What Does It Mean to be HIPAA Compliant?
By Joaquin Lozano
September 28, 2021
The Health Insurance Portability and Accountability Act (HIPAA) is a set of regulations that dictate how to lawfully use and disclose individuals’ protected health information (PHI). The Department of Human Health and Services mandates that all covered entities and business associates operate in compliance with HIPAA. Organizations that create, transmit, or collect PHI electronically, such as health insurance providers, fall under the umbrella of covered entities. Organizations that perform contract work for a covered entity and encounter any form of PHI are classified as business associates. It is important for all required organizations to comply with HIPAA, otherwise, the welfare and privacy of the general public could be jeopardized. Single Sign-Ons (SSOs) offer a solution that can make it easier for entities to comply with HIPAA regulations, by providing safer, more manageable methods of security.
Why is HIPAA Compliance Important?
HIPAA is the primary federal law responsible for ensuring the protection of health information. This act consists of a series of regulatory standards that establish the lawful use and disclosure of PHI. Names, phone numbers, addresses, social security numbers, financial information, medical records, and more are all classified as protected health information. The compromise of PHI can contribute to improper use, identity theft, misinformation, health problems, and more. Hence, it is critical that businesses and organizations comply to guarantee the protection of PHI.
HIPAA Rules
There are four major rules that businesses must be aware of to remain compliant. The first is the Privacy Rule, which only applies to covered entities. This rule includes patient’s rights to PHI, healthcare provider’s rights to deny access to PHI, as well as the contents of Use and Disclosure release forms and Notices of Privacy Practices.
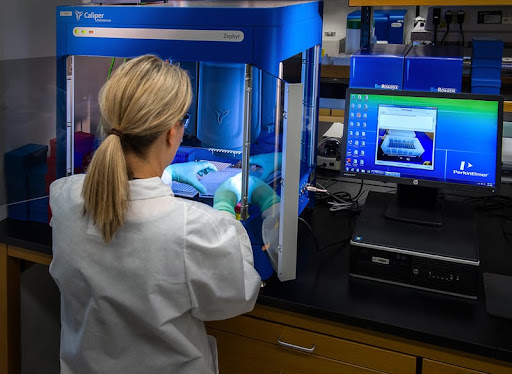
The second rule is the Security Rule. This rule applies to both covered entities and business associates. It establishes guidelines for the proper handling, transmission, and management of electronic protected health information. It is the chief rule governing practices involving ePHI, requiring covered entities and business associates to maintain reasonable and appropriate physical, technical, and administrative safeguards.
The third rule is the Breach Notification Rule. It contains all regulations that both covered entities and business associates must adhere to in the event of data breaches containing PHI or ePHI. All data breaches must be reported to the U.S. Department of Health and Human Services (HHS) Office for Civil Rights (OCR), but the specific reporting protocols vary according to the size of the breach.
The fourth rule is the Omnibus Rule, which is actually an addendum to HIPAA that requires that not only covered entities comply with HIPAA, but also business associates. It outlines the procedures for developing contracts between business associates and covered entities, allowing for the transmission of PHI AND ePHI.

HIPAA Compliance Requirements
The Security Rule lays out safeguards for covered entities and business associates. They fall into three categories: administrative, physical, and technical.
Administrative Safeguards
- Security Management Process: Covered entities must evaluate potential risks to ePHI, implement security measures suitable for preventing the identified risks, document which security measures were adopted, and continue to maintain the security protections.
- Security Personnel: Covered entities must appoint an official who will head the development and implementation of security practices.
- Information Access Management: Covered entities must implement policies and standards for the authorization required to access ePHI and PHI.
- Workforce Training and Management: A covered entity must properly train workforce members regarding practices and policies relating to ePHI and PHI. Covered entities must have sanctions for policy violations and they must be applied when necessary.
- Evaluation: Periodically, covered entities must assess the effectiveness of their security measures in fulfilling the requirements of the Security Rule.
Physical Safeguards
- Facility Access and Control: Covered entities must restrict the unauthorized access of their facilities, while making it accessible to those with the proper authority.
- Workstation and Device Security: Covered entities must institute policies and procedures for access to, and proper utilization of workstations and electronic media.
Technical Safeguards
- Access Control: Technical policies must be in place to guarantee that only authorized personnel are granted access to ePHI and PHI.
- Audit Control: Hardware, software, and/or procedural mechanisms must be implemented so that covered entities may record and examine activity on information systems containing ePHI.
- Integrity Controls: Policies and procedures must be implemented to prevent the unauthorized alteration or destruction of ePHI.
- Transmission Security: Covered entities must have technical protections that defend against the compromise of ePHI that is transmitted electronically.
SSO Compliance with HIPAA
It can be quite a challenge to maintain HIPAA compliance, as the systems in use are oftentimes costly and difficult to manage. However, single-sign on (SSO) technology offers useful tools that can be used to sustain compliance more easily. The employment of an SSO can provide numerous benefits to covered entities and business associates that will aid in adherence to the guidelines set forth by the Security Rule. SSOs can satisfy HIPAA requirements cited in the “Person or Entity” section by implementing a system of strong authentication, so that only the correct user may be granted access upon logging in. They can further improve security by encouraging stronger, more complex passwords, since users are only required to remember a single set of credentials. SSOs can also aid in the organization of employees and their work, by eliminating the need for shared accounts and creating unique account logins for each individual. HIPAA requires an audit trail of every individual who accesses ePHI and PHI. An SSO can facilitate the recording of the organizational data necessary for an audit, such as which accounts have access to the specified applications, by automatically storing data when user activity occurs.
humanID is a non-profit SSO provider offering a solution that doesn’t save any of the users’ personal data. The only information saved with humanID is the unique hash generated when users input their phone number. The phone number is immediately deleted following the verification, ensuring that the only information that users transmit is the information that they meant to transmit. Like other SSOs, humanID aims to grant convenience and security to its users. However, humanID provides enhanced security that can properly protect and serve to prevent unauthorized access and transmission of ePHI.
As the primary federal law regulating the security of protected health information, HIPAA makes it difficult for PHI to be compromised by mandating that all covered entities and business associates adhere to its standards. This can provide quite a bit of work for entities to remain compliant, and SSOs, like humanID, provide solutions that can mitigate some of the hardships.


