Top Four Ways to Protect User Privacy
By Alice Zhang
March 1, 2021
Hundreds of millions of emails, phone calls, app downloads, and user accounts are made each day, with the numbers only rising. With increasing news reports on data breaches, government tracking, and even personal targeted attacks, protecting user privacy has become an inevitable issue. In the Digital Age, consumers are constantly susceptible to such dangers. Only a combination of rigorous industry efforts and federal policies can provide consumers with the security they need.

Here are four ways we can protect user privacy:
1. Be aware of industry and government guidelines
As with any topic, one must be aware of both the required and recommended government guidelines pertaining to user privacy. The Federal Trade Commission, for example, provides the public with information on its regulations and enforcement policies. In addition, the FTC also conducts research, holds workshops, and creates reports on relevant topics. Such reports may range from recommendations on protecting user privacy with mobile applications and products to general recommendations to businesses and policymakers regarding data privacy and protection guidelines. Additionally, the California Consumer Privacy Act (CCPA) has allowed consumers to have greater control over their personal information. The CCPA provides consumers with the right to be informed, delete, opt-out, and to non-discrimination in regards to the use of their data. Several other notable examples of policies protecting user privacy are Europe’s General Data Protection Regulation (GDPR) and the 2018 law Vermont passed requiring data brokers to allow individuals to opt-out of personal data collection.
2. Minimize and protect: collect data only when needed and protect the data you need
Some types of data are required for basic functionality; however, it is best to minimize the data collected continually to safeguard user privacy. humanID does not store any type of personal identifying information; our single sign-on (SSO) allows users to sign onto multiple applications and websites with only SMS verification, hashing and deleting the user’s phone number immediately after initial verification.
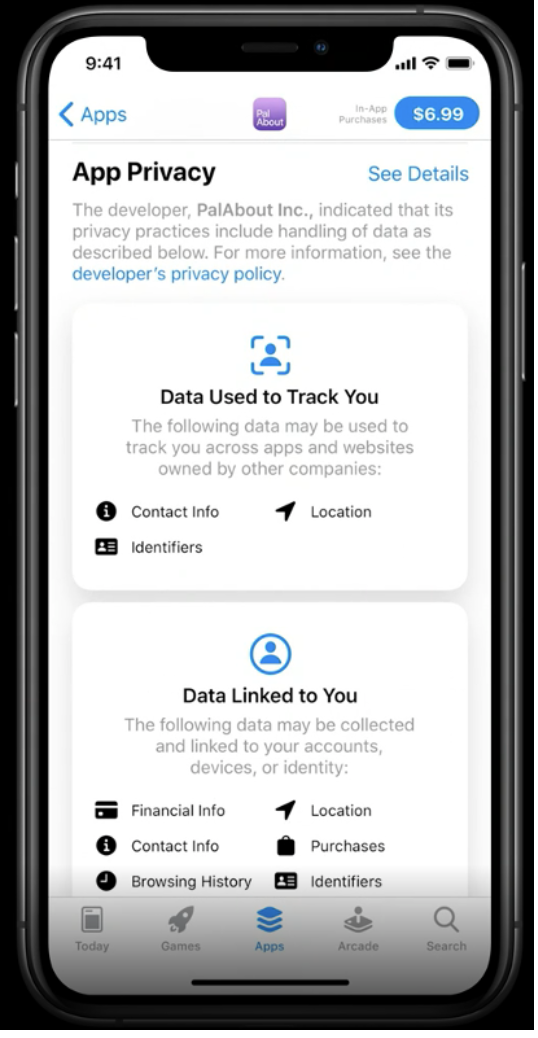
Generally, when it is necessary to request user data, practice providing users with technical documentation or some sort of explanation as to why the data being requested is necessary. As an example, Apple provides a purpose string when asking users for personal information such as location, addresses, and phone numbers. Just like its title says, the purpose string Apple uses serves to inform users with how and where their data will be stored and used. Similarly, Google uses a similar method when trying to preserve user privacy and asking users for data, making its user data policy easily accessible to developers. It is also important to set encryption safeguards when storing data.
As mentioned earlier, humanID deletes each user’s data immediately after verification, therefore avoiding the mass security breaches allowing hackers to gain access to millions of accounts companies like Facebook have suffered from. More specifically, humanID uses two levels of hashing to protect our users’ privacy to the highest standards. In the first level, the phone number each user provides us is hashed and salted. Then the salted hash is stored and the user’s plaintext phone number is immediately deleted. In the second level, each user is sent a hash specific to the platform they are signing up for after SMS verification. This hash is the client’s username specific to that platform. Each user will have different hashes sent to each platform they sign up for to protect their anonymity. In this way, users can safeguard their private information while signing up for anything from mobile games to VPNs.
3. Maximize Client Autonomy
As consumers, we instinctively favor providers who offer us more freedom in our choices, even if our decisions are as trivial as switching over to a new television provider. User privacy, in regards to data transmitted, is no different. Aside from following the general guidelines to minimize the amount of user data collected, it is equally important to allow clients or users to have the utmost choice when it comes to their privacy. One basic strategy employed by several mobile tech companies is to provide users with easily accessible and adjustable privacy settings. In this way, users have direct control and access to the data being shared and, thus, greater autonomy. With humanID’s SSO, users have direct autonomy over their private data as we do not store or distribute any personal or device information.
4. Promote transparency in data usage
Just as we see transparency and honesty in relationships as symbols of both respect and understanding, transparency in terms of user data usage is crucial to building strong and lasting relationships with clients. Promoting transparency can be as simple as making the company privacy policy documents and resources available and easily accessible through URL links. It is even better to describe and/or summarize the company’s privacy policy in the mobile app description or on the website. As an open-source platform, humanID aims to remain transparent in our dedication to promoting user privacy. Not only is our technology made available to all, but our company policies are centered around transparency among our team and our clients.
Ultimately, a fierce dedication to protecting user privacy is not only recommended but a necessity for building lasting relationships with clients in today’s day and age. For a trusted social login option with an organization that not only follows but is built upon these guidelines, turn to humanID.



Very efficiently written article. It will be useful to anybody who usess it, including yours truly :). Keep up the good work – can’r wait to read more posts.